Revolutionizing Cybersecurity with HumanAuthn
Prevent data breaches, identity theft, and database hacks with HumanAuthn — the world’s first authentication and encryption layer that returns full data custody to the individual.
INTRO
The Future of Data Security is Here - HumanAuthn
Start Encrypting Sensitive Data With Biometrics.
Every day, hackers sharpen their tools to exploit sensitive and private data of end users. For banks, e-commerce giants, fintech innovators, and digital enterprises, a single breach can mean catastrophic financial loss, legal penalties, and eroded trust.
Secure your sensitive data with HUmanAuthn – the world’s first cybersecurity solution to combine, authentication, data encryption and zero-knowledge disclosure with facial recognition to ensure both privacy and protection.
HumanAuthn
Verify identities without biometric templates or storing facial data.
Enterprise-Grade Liveness Detection
Defeat deepfakes, 3D masks, and photo spoofs.
Blockchain Storage
Move sensitive user data to the blockchain and never worry about data breaches again.
Data Ownership
Give Users full control and custody of their data.
Effortless Global Compliance
Meets GDPR, PCI-DSS, PSD2, and other key regulations.
Security will come not from
a patchwork but an architecture
-George Gilder, Life after Capitalism
PROBLEM
Data Breaches - An Ever Growing Security Threat
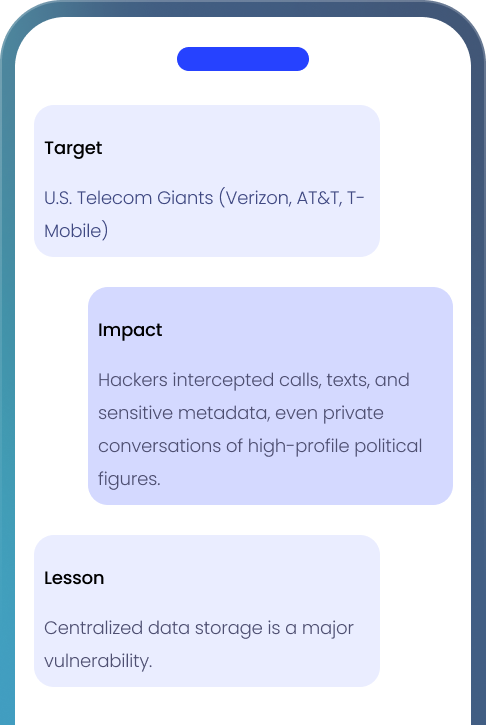
1. Worldwide – The Salt Typhoon Attack (2024)
Data of millions of users was compromised in over 200 organizations across 80 countries
2. Japan – Asahi Glass (2026)
Black Basta claimed to have stolen 1.5 TB of data from this Japanese company.
3. United Kingdom — Government data base (2026)
South Gloucestershire Council, a UK government entity was victim of data leak
4. Spain — Financial data base (2026)
IBAN Financial data amounting to 21 millions citizens was leaked.
5. Spain — Endesa / Energía XXI (2026)
The personal data of 20 million citizens amount to 1.05 TB of data was leaked.
How ZK Face Proof Protects You:
Eliminates centralized storage of sensitive data.
Zero-Knowledge authentication eliminates single point of failure
Even if hackers infiltrate, they find nothing to steal.
How ZK Face Proof Protects You:
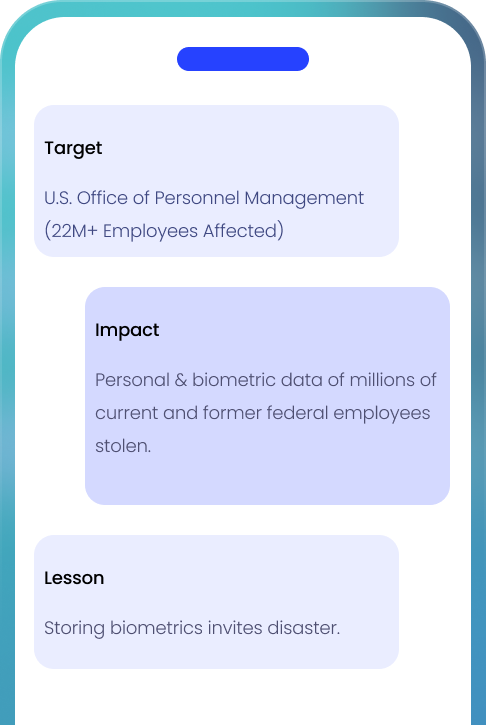
No biometric data storage = no risk of reverse engineering.
Elliptic Curve Cryptography (ECC) ensures total user control.
Prevents breaches that could expose personal identities.
SOLUTION
Protect Personal Data With Biometric Encryption
Traditional databases store and encrypt all types of data within the same architecture, creating centralized targets that are highly attractive to cybercriminals.
HumanAuthn applies biometric-bound encryption to the most sensitive data, significantly increasing the cost and complexity of an attack.
Users’ data should belong to users — not hackers.
Integrate
Developer-friendly API with pre-built SDKs for seamless adoption.
Scale
From 100 to 10M+ verifications/month with zero downtime.
No Overhead Costs
Eliminate the use of databases and servers.
INDUSTRIES
Uncompromising Security for the World’s Most Targeted Industries
HumanAuthn API uses state-of-the-art facial recognition technology combined with zero-knowledge disclosure for enhanced privacy. It securely verifies user identities without compromising personal data. By adopting this solution, your business gains an additional layer of cybersecurity that’s impossible to crack, even for the most advanced hackers.
For Banks & Fintechs
Users will have full ownership & custody of their banking data
Secure KYC/AML onboarding with encrypted facial authentication
Complete protection against large-scale breaches like Salt Typhoon

For E-commerce & Digital Platforms
Protect customer profiles & payment data with no storage authentication
One-click, zero-risk checkouts with facial authentication
Say goodbye to hacks like the OPM breach, where massive PII was stolen
For Healthcare & SaaS
GDPR-compliant user verification without storing medical records
Ensure full patient data privacy with zero-knowledge security
Future-proof your system against healthcare cyber attacks

NEW ARCHITECTURE
A New Cybersecurity Architecture is Needed
User’s data are all in a relatively few target-rich sites, the potential hackers number in the billions, anonymous and ethereal.
New users bring new vectors of possible attack. Every new user is a possible hacker or hack victim. Software patchwork—grows only additively. It stops one attack vector at a time. Meanwhile attack vectors expand exponentially.
This is not a problem that can be solved with one more privacy patch or even by doubling the money spent on cybersecurity.
The more we spend on internet security, and the more we expand the network, the more vulnerable it grows.
Gilder, George. Life after Capitalism

Act Now—Before the Next
Breach Headline
Tomorrow’s Breach is Planned Today. Are You Ready?
Frequently Asked Questions
Still Have Questions?
Our security experts are ready to show you how ZK Face Proofs can transform your security infrastructure.