Unbreakable Database Security at Your Disposal
Your Database is Only as Secure as Your Method of Storage.
The weakest link in security is centralized architecture. Data breaches and hacks are a recurring theme due to conventional database security. HumanAuthn, the world’s first biometric-bound encryption system that ensures only verified, live users— encrypt and decrypt their own data in a distributed manner.
INTRO
Why Databases Get Hacked
Stop Storing Sensitive Data. Start Securing Trust.
Cybercriminals don’t look just for data, but for sensitive and private data. Current databases often store public, sensitive, private, and confidential data using uniform methodologies, which can contribute to data breaches in industries such as telecommunications, banking, and e-commerce.
Centralized Databases Are Vulnerable – A single break in can expose millions of records.
Software Patches Signals Architectural Flaws – Cybersecurity budgets keep increasing, but so do data breaches.
Passwords Are Easy to Hack – Phishing, brute-force attacks, and social engineering are effective methods to hack user’s data.
The problem isn’t encryption.
The problem is custody.
HumanAuthn
HumanAuthn: Redefining Trust Architecture
Biometric Encryption. Zero-Knowledge Disclosure. Self-Custody Data.
Hackers target centralized databases because identity and data custody are concentrated in one place. Even encrypted cloud storage remains vulnerable when the encryption keys and authentication layer are device-bound or custodial.
HumanAuthn eliminates this structural weakness.
Instead of storing biometric templates or relying on device-based private keys, HumanAuthn reconstructs ephemeral cryptographic keys through live face recognition and randomness — enabling Proof of Humanity without exposing biometric data.
Sin plantillas biométricas
Sin bóvedas centralizadas de identidad
Sin secretos reutilizables de autenticación
Comparison
HumanAuthn
Others
Device independent
Zero biometric templates used
Ephemeral keys
100% proof of humanity
Zero Knowledge Disclosure
Benefits
Why Choose
HumanAuthn?
Self-Custody Data
With HumanAuthn, users own and control their data ensuring privacy.
Database Agnostic
HumanAuthn can be stored in DBs, IPFS or blockchain eliminating single failure points.
Private Encryption
Elliptic curve cryptography protects sensitive data including biometrics.
Offline / Online
Works with or without internet connection ensuring flexibility and security.
Global Compliance
HumanAuthn meets GDPR, PCI-DSS, PSD2, and other major data security standards, making it easy to operate.
Why Databases Get Hacked
Stop Storing Sensitive Data. Start Securing Trust.
Cybercriminals don’t look just for data, but for sensitive and private data. Current databases often store public, sensitive, private, and confidential data using uniform methodologies, which can contribute to data breaches in industries such as telecommunications, banking, and e-commerce.

HOW IT WORKS
How HumanAuthn Works
Protect the personal data of your users

User Initiates Onboarding

A user accesses a platform, chooses a username and proceeds to register their personal information.
Live Face Scan & KYC

The system captures a real-time facial scan while detecting deepfake and spoofing attempts.
HumanAuthn QR Code

Without sharing raw biometric data, an encrypted cryptographic verifiable credential of the user's personal data is created in the form of a QR code.
Instant Verification & Ongoing Access

The user's biometrics decrypts the QR code to grant access in seconds—without ever exposing sensitive data.
The Data is Safely Stored

Every user gets a HumanAuthn QR code. This code can be safely stored in any database architecture, but it can only be decrypted by the data subject —enabling GDPR compliance.
HumanAuthn delivers seamless, unbreakable data management—without the risks of traditional data storage.
INDUSTRIES
Seamless Cybersecurity for High-Risk Industries
Frictionless User Verification with Privacy-First Authentication
HumanAuthn brings the highest level of security to industries where identity fraud and data breaches are common. By eliminating biometric storage and using zero-knowledge disclosure, it ensures secure authentication with just a password (optional) and simple facial scan—no data risks.
Telecom – Stop SIM Swap Fraud & Fake Activations
Weak identity checks lead to SIM swap fraud and unauthorized activations. HumanAuthn stops fraud before it happens.
- Secure SIM Registrations – Verify users with real-time facial authentication.
- Prevent SIM Swap Attacks – No more hijacked numbers or unauthorized transfers.
- Reduce Fraud Costs – Minimize identity-related customer disputes.
Banking & Fintech – Fraud-Proof KYC & Transactions
Financial institutions face increasing risks from identity theft and compliance failures. ZK Face Proof ensures secure, seamless KYC and transactions.
- Instant KYC Without Risk – Verify users without storing biometric data.
- Secure Payments & Logins – Authenticate transactions with a quick facial scan.
- Regulatory Compliance – Meets GDPR, PSD2, and financial security standards.
E-Commerce – Secure Logins & Frictionless Checkouts
Account takeovers and payment fraud can devastate online businesses. HumanAuthn protects e-commerce platforms with real-time user verification.
- Robust Logins – Eliminate weak passwords break in with secure facial authentication.
- Stop Payment Fraud – Approve transactions only for real, verified users.
- Enhance Customer Trust – Reassure buyers their biometric data is never stored.
INTEGRATION
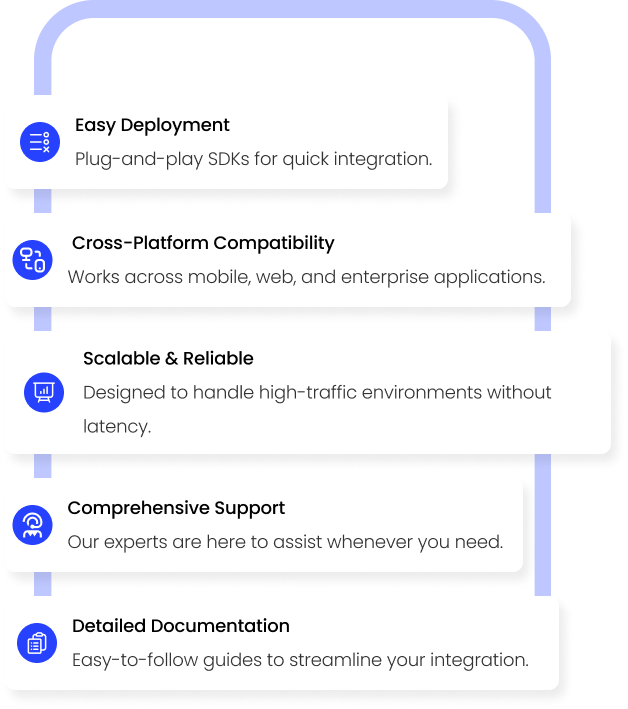
Effortless Integration, Maximum Security
Plug, Authenticate, Secure
HumanAuthn fits right into your existing systems with our developer-friendly API. Whether you’re running a banking app, an e-commerce platform, or a telecom authentication portal, integration is fast, flexible, and hassle-free.
Your Database. Your Rules. No Unauthorized Entry
Don’t let hackers exploit weak authentication. With HumanAuthn, access is granted only to those who truly belong.